These Chrome Extensions Are Stealing Your Data – Uninstall Them Immediately
A new report by Socket showcases the potential dangers of downloading browser extensions, with grander implications for the broader security landscape. These 108 malicious Chrome extensions disguise themselves as useful applications, ranging from games and utilities to social media sidebars. However, despite posing as legitimate applications, the extensions inject code into the background of users' browser sessions. These browser incursions result in hackers stealing user information and injecting ads and malicious JavaScript into every website users visit. Here's the full list of extensions identified by Socket. Extensions with more than 1,000 downloads include:
- Web Client for TikTok
- Web Client for Telegram – Teleside
- YouSide – Youtube Sidebar
- Web Client for Youtube – SideYou
- Formula Rush Racing Game
- Page Auto Refresh
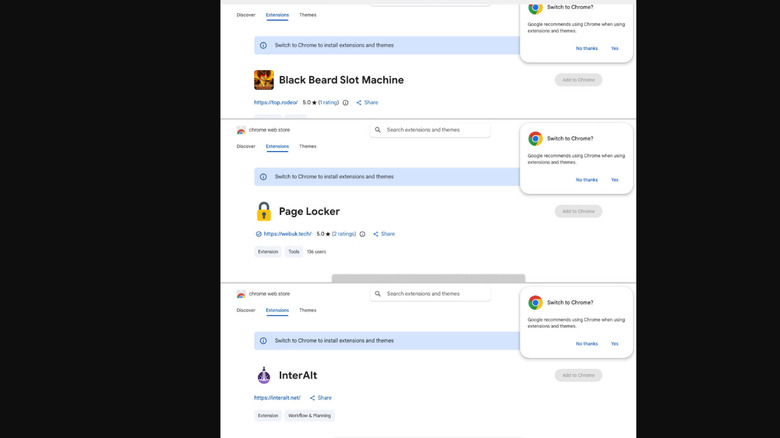
- Page Locker
- Text Translation
- Web Client for Rugby Rush – SideGame
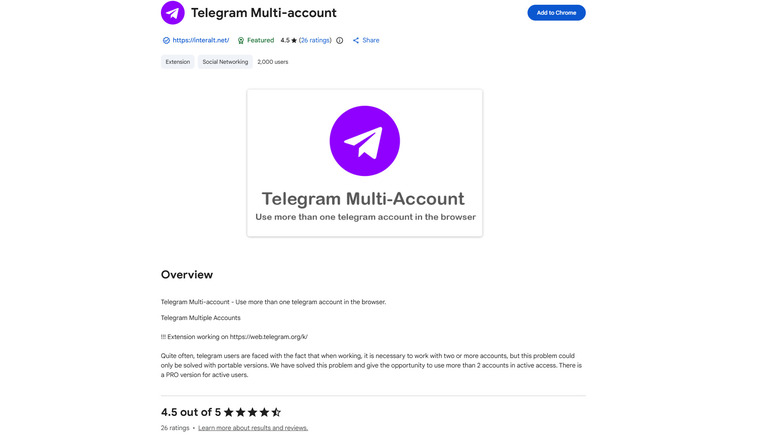
- Telegram Multi-account
- Black Beard Slot Machine
- Clear Cache Plus
- Speed Test for Chrome – WiFi SpeedTest
Experts suggest immediately removing any of these extensions from your Chrome web browser. To do so, click on the three dots in the top right corner of your browser window. Next, hover over the menu item that says "Extensions" and select "Manage Extensions." If any of the 108 malicious extensions listed in the Socket report appear in the Manage Extensions window, you should delete them.
Furthermore, users are encouraged to log out of all Telegram web and mobile sessions. Users can do so by going to the "Devices" section of their Telegram settings. Meanwhile, users who signed into the game and sidebar extensions are likely to have exposed their Google account and should review third-party access by visiting myaccount.google.com/permissions.
These extensions were part of an elaborate scheme
The scheme used a variety of seemingly legitimate applications to target a wide swath of victims. Extensions included text translators, page utility extensions, Telegram sidebars, slot machine and Keno games, and social media enhancers. The 108 attack vectors were spread out across five "distinct" publishers: GameGen, Yana Project, Rodeo Games, InterAlt, and SideGames.
However, Socket found that these extensions shared backend architectures, indicating a single point of origin. For instance, all 108 extensions were linked to a single command-and-control (C2) server, indicating that the servers housing victims' stolen data were "controlled by the same operator." Furthermore, the five publishers shared Google Cloud project numbers, providing researchers "the strongest single piece of evidence for unified ownership." The attackers' identity remains uncertain. However, Socket identified Russian language comments across the extensions' source codes, potentially indicating a country of origin.
Of the 108 add-ons, 54 targeted users' Google account identities. Such applications are particularly dangerous, as they not only harvest users' Gmail address, name, and profile picture, but the unique account identifier. Also known as a sub ID, this identifier acts as the account's unchangeable digital fingerprint, allowing hackers to build a more in-depth profile when targeting victims. 45 of the extensions added universal backdoors into users' Chrome web browsers, which opened automatically upon starting the browser. Telegram session theft is another major concern. One of the most "severe" attacks comes from an extension known as Telegram Multi-account, which exfiltrated Telegram Web sessions every 15 seconds. The remaining extensions engaged in a variety of malicious behaviors, ranging from stripping social media security headers to injecting ads into visited websites.
This isn't the first time malicious Chrome extensions have targeted users
The impact of the scheme is likely extensive. Although the download metrics for individual extensions only number in the low thousands, the network's collective reach is wideranging. At the time of Socket's reporting, roughly 20,000 users were affected by the scheme. Over 3,000 of said downloads targeted the victims' Telegram accounts. According to Socket, the scheme was likely "operated as a Malware-as-a-Service platform," meaning victims' "stolen identities and sessions are accessible to whoever purchases access." The "payment portal and the per-user system" used in the extensions' C2 infrastructure attest to these assumptions and give indication to the likely uses of victims' data. Socket's security team alerted Google to the dangers posed by the scheme's various extensions. However, to date, many of the extensions continue to operate, even sometimes retaining their "featured" status on Chrome's Web Store.
Over the past few years, browser extensions have become an increasingly popular means of attack for hackers. One 2025 attack, for example, used 33 browser extensions to pilfer sensitive data from some 2.6 million unwitting victims via the Chrome Web Store. The trend has begun to spill over into the artificial intelligence realm, as security professionals have found threat actors targeting users via phone chatbot extensions, impersonating popular AI brands to capitalize on the proliferation of AI browser extensions. Security experts warn that extensions are a particularly easy means for hackers to access your browser.
The report is a reminder to remove any suspicious or unnecessary extensions. To protect yourself from future threats, opt for well-established brands when possible and always review the security permissions of an extension before downloading. Other safety precautions, like subscribing to a strong antivirus software and enabling Enhanced Safe Browsing, can also be a security boon.